New Release: The Gorilla Guide® To… Practical Endpoint Privilege Security
You can’t trust your staff. Not because they’re bad people—well, actually, malicious attacks from insiders do occasionally occur. But the much greater problem is an outsider who gains access to your secure network by subverting an employee’s account.
Many threats escalate from compromising a single user account to disabling entire networks—an email phishing attack that leads to the installation of ransomware, for instance. You can expect that employees will innocently fall victim to malware. What you need to do is prevent the attacker from using their newly gained access to reach sensitive systems and data
In The Gorilla Guide® To… Practical Endpoint Privilege Security, James Panetti describes the vulnerabilities in typical organizational computer systems. He explains the roles played by traditional security measures such as firewalls or endpoint detection and response (EDR), and why they need to be bolstered by endpoint privilege security (EPS).
EPS applies the classic principle of least privilege with a small computing footprint. Using fine-grained security practices such as role-based access control (RBAC), EPS protects your critical systems and data from attacks coming from user accounts you normally trust. It notices when a suspicious activity is requested (Figure 1) and blocks it.
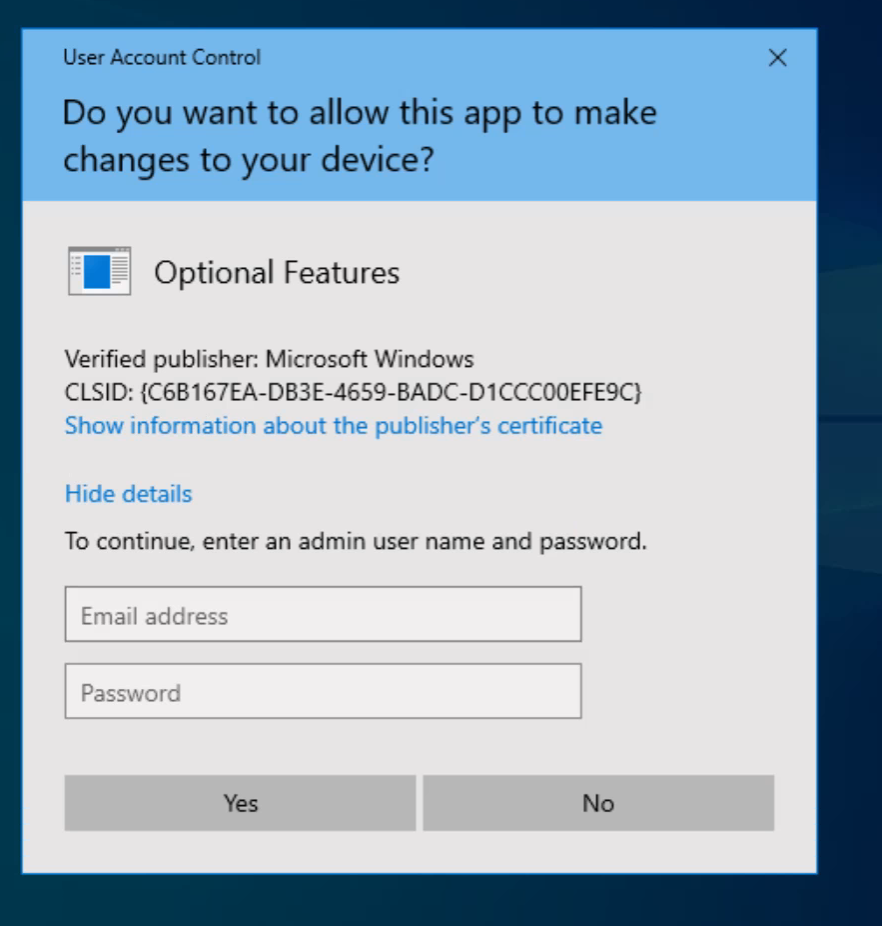
Figure 1: Example of a UAC prompt in Windows
Panetti also describes the efforts you need to take to make EPS effective, and the value of CyberArk’s Endpoint Privilege Manager (EPM) service.
Inside the Guide
Gorilla Guides make learning and discovery approachable and easy, and they take the guesswork out of navigating complicated IT technologies. Written by an industry expert, and brought to you by ServiceNow, this resource is packed full of trusted information about endpoint privilege security!
Download the book and learn all about:
- Endpoint Privilege Security Compared to Verdict-Based Security and to Endpoint Detection and Response
- Vulnerabilities That Allow Privilege Escalation in Windows
- Why Fine-Grained Access Can Preserve Productivity While Strengthening Security
Table of Contents
Chapter 1: Endpoint Privilege Security: A Primer
- What Is Endpoint Privilege Security?
- Why It’s Important: Case Studies
Chapter 2: Access-Based Security
- Regarding Verdict-Based Security
- Implementation Examples
- Protection from Cyberattacks
Chapter 3: Practical Endpoint Privilege Security
- Remove Local Administrator Access
- Enforce the Principle of Least Privilege
- Defend Credentials, Cookies, and Security Tokens
- Why It’s Often Neglected
Chapter 4: How EPS Fits Your Broader Security Strategy
- A Pillar of Identity Security
- Reinforcing Access to Sensitive Data
- EPS vs. EDR
Chapter 5: CyberArk Endpoint Privilege Manager
- Multi-Platform
- Built-in Security
- Preserve Productivity
- Cutting-Edge Technology
- Get Started with CyberArk Endpoint Privilege Manager
- Stay Cyber Secure
About The Author
James Panetti is a tech industry veteran, writer, and owner of Panetti Tech Insights. He became a writer and entrepreneur after a long career providing support and consulting services under the employ of companies the likes of Oracle, CA Technologies, and Broadcom. He spends his free time as a tech hobbyist, creative writer, and podcast co-host of Little Podcast of Horrors.
About CyberArk
CyberArk is the first and only leader in both Gartner® Magic QuadrantTM Reports for Access Management and PAM ever. Gartner evaluated more than 20 vendors across the two reports, and CyberArk is the only Leader in both Access Management and Privileged Access Management.
Download…