New Release: The Gorilla Guide to…® Secure IT for Small and Midsize Businesses, Express Edition!
Much lip service is given to IT security, yet breaches and ransomware attacks routinely make the headlines. The gap between aspiration and true security is often due to the difficulty and expense of viable security.
True computer security experts are expensive and hard to find. Current trends—notably access to apps through mobile devices and remote work—present a landscape for attack that is widely spread out and scattered. New threats keep popping up, taking advantage of flaws in sophisticated third-party software. Encryption and other security measures add overhead that hurt performance and response time unless you use specialized cloud solutions, such as Flash arrays.
All these burdens fall hard on large businesses, and even harder on small and medium sized businesses (SMBs). No wonder it’s easiest to check off a few security boxes and hope that nothing goes wrong.
The Gorilla Guide To…® Secure IT for Small and Midsize Businesses lays out the risks of lax IT security and presents reasonable actions an SMB can take to improve security. For instance, you don’t have to set up a single network bringing together all your assets and employees. You can divide your network logically into different segments for different purposes using Instant On, a product of Aruba, a subsidiary of Hewlett Packard Enterprise (HPE).
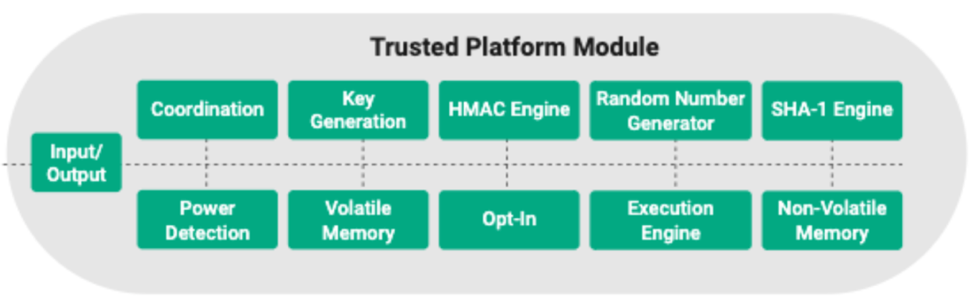
Some of the key technologies covered in this report are two-factor authentication, virtual private networks (VPNs), virtual desktop infrastructure (VDI), the importance of security at the edge, and the Trusted Platform Module (TPM) concept illustrated in Figure 1.
With examples from HPE, The Gorilla Guide To…® Secure IT for Small and Midsize Businesses shows the strategies and planning required to achieve end-to-end IT security and reliable disaster recovery.
Inside the Guide
Gorilla Guides make learning and discovery approachable and easy, taking the guesswork out of navigating complicated IT technologies. Written by an industry expert, and brought to you by Hewlett Packard Enterprise, this resource is packed full of trusted information about reliable end-to-end security for SMBs!
Download the book and learn all about:
- Levels of Security (Server, Network, etc.)
- Secure Solutions for Employee Access, Backups, and More
- What Disaster Recovery Entails
Table of Contents
Introduction: Secure IT Is Not Optional
Chapter 1: SMB Security Can Be Difficult (and Costly)
- No Shortage of Security Trouble for SMBs
- The Ever-Spreading SMB Boundary
- HPE Security Solutions
- Baked-in Security at the Edge
Chapter 2: New Security Challenges for SMBs
- Secure Networks Deliver Secure Operations
- Enable Secure WFH Productivity
- Secure, Reliable File Backup—and Restore
Chapter 3: Business Continuity Is Increasingly Critical
- The Many Faces of Business Continuity
- Paths and Mechanisms for Business Recovery
- Putting Business Continuity to Work
Chapter 4: HPE Provides Built-in Security for SMBs
- What Security Means in 2021
- Silicon Root of Trust
- Trusted Platform Module (TPM)
- HPE’s Trusted Supply Chain
- HPE Covers the Full Range of SMB Security Needs
Download Your Copy!
About the Author
Ed Tittel is a 30-plus year veteran of the IT industry who writes regularly about cloud computing, networking, security, and Windows topics. Perhaps best known as the creator of the Exam Cram series of certification prep books in the late 1990s, Ed writes and blogs regularly for GoCertify.com, TechTarget, ComputerWorld, and other sites. For more information about Ed, including a resume and list of publications, please visit EdTittel.com.
About Hewlett Packard Enterprise
Grow your business with small business IT solutions that power your key ambitions and help you achieve big goals. Explore how HPE small business IT solutions can best serve your small and midsized business needs. www.hpe.com/smallbusiness
Download the guide here!